Database Protection
Stop SQL Injection Inside the Application
Prevent SQL injection at execution time - before malicious queries ever reach the database.
Book a demo
SQL Injection In the AI Era

Obfuscation Wins
Attackers evade signature-based tools with AI encoding & obfuscation

WAF Blindness
WAFs can’t see what executes once traffic is allowed

AI Makes It Worse
AI generates infinite SQLi variants that bypass rules instantly
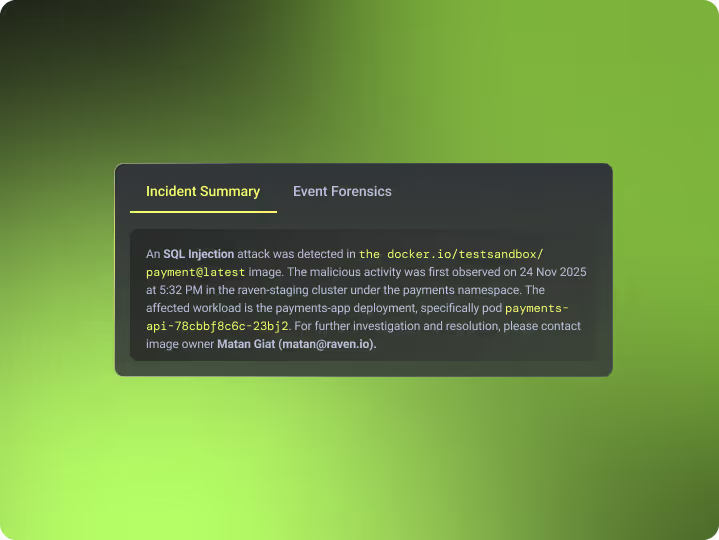
In-Application SQL Injection Prevention
Raven prevents SQL injection from inside the application, by monitoring the SQL client libraries that actually generate and execute database queries.
No network traffic inspection. No signatures or rules.
Raven observes how queries are constructed and executed in real time, and blocks malicious execution at the source.
No network traffic inspection. No signatures or rules.
Raven observes how queries are constructed and executed in real time, and blocks malicious execution at the source.
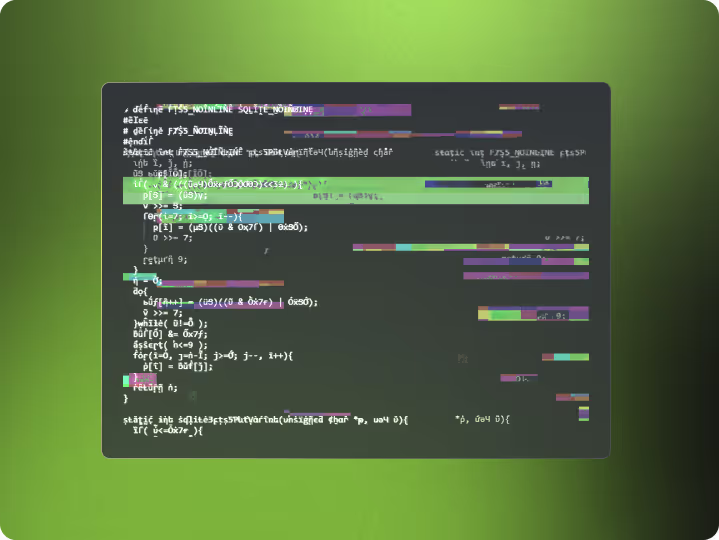
Obfuscation-Proof by Design
Raven operates after the query is constructed, at execution time inside the application - not at the network edge. This makes Raven immune to query obfuscation, encoding tricks, parameter smuggling and AI-generated payloads.
If the execution is malicious, it’s blocked.
If the execution is malicious, it’s blocked.
Zero Rules. Zero Maintenance.
Traditional SQL injection defenses require constant rule updates, new signatures and emergency tuning after bypasses.
Raven requires none of that.No rules to write.
No signatures to maintain. No tuning for new attack techniques.
Protection adapts automatically because it’s based on runtime execution behavior, not static detection logic.
Raven requires none of that.No rules to write.
No signatures to maintain. No tuning for new attack techniques.
Protection adapts automatically because it’s based on runtime execution behavior, not static detection logic.
Rule-less Detection
No signatures. No allowlists. No maintenance.
Execution-Level Accuracy
Detects SQL injection other tools cannot see.
<0.2% CPU Overhead
Safe to run in high-throughput production systems.
See SQL Injection Blocked at Execution Time
Book a demo
Security
SAST scans source code for vulnerabilities before deployment. Learn how it works, what it finds, and the blind spots it leaves open in production.
Read more
Security
SAST scans your code. SCA scans open source dependencies. Learn the differences, what each misses, and why runtime SCA adds the missing layer.
Read more
Security
SCA scans open source dependencies for known CVEs. Learn how it works, why it generates so much noise, and how runtime SCA shows what actually matters.
Read more

.svg)
