Runtime ADR
Protect the application from within
Raven ADR, runs inside the application, detects real application attacks as they execute, with deep, library and function-level forensics that traditional tools never see.












Attacks Hide Inside Application Logic Where EDR Cannot See
Modern attacks abuse legitimate libraries, frameworks, and execution paths, blending into normal application behavior. Zero day attack detection requires visibility into execution paths, not network patterns. Infrastructure and network-level tools miss this entirely.
Traditional Detection Tools Miss Application-Layer Security Attacks
EDR, CWPP, and WAF tools see processes, files, and network events - not why code executes or how execution flows through the application. Without application-layer security context, alerts are noisy and response is slow.
Language Sprawl Increases Application Attack Surface
Companies run applications across an average of nine programming languages. Real runtime application security requires a solution that works across all languages without language-specific agents, custom instrumentation, or manually maintained detection rules.
Features
Application. Detection. Response
True Application-Level Visibility: The Foundation of ADR Security
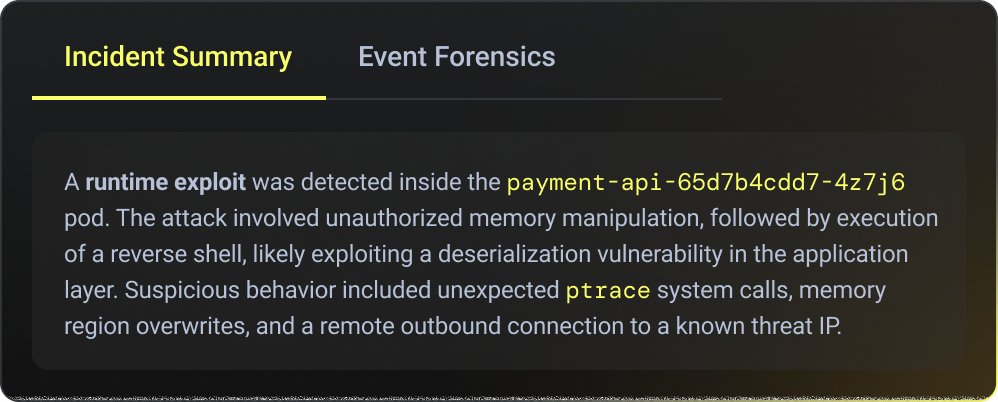
Raven provides runtime application security and application security monitoring by observing real execution inside the application down to libraries, functions, dependencies, and call paths. This runtime visibility replaces log-based guesswork and behavioral heuristics with precise execution data that enables accurate detection, investigation, and response.

Library-Level Forensics for Runtime Threat Detection
Built on eBPF and Raven’s patented library-level monitoring technology, Raven delivers runtime threat detection by capturing every execution as a deterministic call flow showing which libraries executed, in what order, and exactly where execution deviated during an attack.
This library-level forensic visibility identifies the precise deviation point in the call chain, enabling faster and more accurate incident response than traditional log correlation approaches.
This library-level forensic visibility identifies the precise deviation point in the call chain, enabling faster and more accurate incident response than traditional log correlation approaches.

.png)
Developer Attribution: Root Cause for ADR Security Investigations
Raven traces runtime attacks back to the exact code change that introduced the risk, mapping every exploit to the owning commit, author, deployment, and service. In ADR security, this developer attribution closes the gap between detection and remediation by turning runtime attack data into actionable engineering context instead of generic alerts.
Security teams see what happened. Developers see exactly where it came from and how to fix it.
Security teams see what happened. Developers see exactly where it came from and how to fix it.
.png)

Runtime Drift Detection: Catch Post-Exploit Persistence and Supply-Chain Abuse
Runtime threat detection requires visibility into real application execution.
Raven detects execution drift in real time by identifying unexpected package installs, unauthorized binaries, anomalous code paths, and runtime behavior changes associated with supply-chain abuse, post-exploit persistence, and living-off-the-land attacks. This drift detection exposes attack techniques that signature-based tools and static indicators cannot reliably catch.
Raven detects execution drift in real time by identifying unexpected package installs, unauthorized binaries, anomalous code paths, and runtime behavior changes associated with supply-chain abuse, post-exploit persistence, and living-off-the-land attacks. This drift detection exposes attack techniques that signature-based tools and static indicators cannot reliably catch.

SQL Injection Detection at Runtime: No WAF Rules Required
Raven detects SQL injection and database abuse from inside the application runtime, not from network patterns or query signatures. This is done by observing real execution paths, input flow, and query construction. This enables high-fidelity SQLi detection with full application context, even for dynamic or obfuscated queries, without regexes, payload guessing, or WAF false positives.

.png)








.png)



Frequently Asked Questions
What programming languages does Raven support?
.svg)
Raven is Language-agnostic by design. Raven works across all major programming languages, without language-specific agents or rules. One model. One view. No blind spots. The program languages supported by Raven: Java (and any JVM based programming language), JavaScript (Node.js), Python, Go, Ruby, C++, C, Rust, PHP, Scala, Kotlin.
Is Raven built for production?
.svg)
Yes! Raven is built for production. Raven is designed to run continuously in high-throughput, real-world production environments. No code injection. No request replay. No data exfiltration pipelines that break at scale.
What is Runtime ADR?
.svg)
Runtime ADR (Application Detection & Response) is a security approach that detects and responds to attacks from inside the running application, based on real code execution - not network traffic, signatures, or known malware patterns.
How is Runtime ADR different from EDR, CWPP, or WAF?
.svg)
EDR, CWPP, and WAF operate outside the application, focusing on processes, files, network requests, or known patterns.
Raven ADR runs inside the application runtime, understanding which libraries and functions executed and how execution flows changed during an attack.
Raven ADR runs inside the application runtime, understanding which libraries and functions executed and how execution flows changed during an attack.
Does Raven ADR rely on CVEs or signatures?
.svg)
No. Raven ADR does not rely on CVEs, signatures, or predefined attack rules.
It detects abnormal execution behavior at runtime, allowing it to identify attacks even when no CVE exists.
It detects abnormal execution behavior at runtime, allowing it to identify attacks even when no CVE exists.
How does Raven reduce false positives?
.svg)
Raven observes actual execution paths - which libraries ran, in what order, and how execution deviated.
This context eliminates guesswork and heuristics, resulting in high-fidelity alerts with statistically negligible false positives.
This context eliminates guesswork and heuristics, resulting in high-fidelity alerts with statistically negligible false positives.
Can Raven ADR help developers remediate issues?
.svg)
Yes. Raven automatically maps runtime attacks back to the exact code change, including the commit, author, deployment, and service.
Security teams understand what happened - developers see where it came from and how to fix it.
Security teams understand what happened - developers see where it came from and how to fix it.
How is Raven ADR deployed?
.svg)
Raven ADR is deployed as a lightweight runtime component and integrates via standard deployment workflows (e.g., Kubernetes, Helm).
It requires no code changes, no code injection, and no request replay, and can be enabled incrementally per service or environment.
It requires no code changes, no code injection, and no request replay, and can be enabled incrementally per service or environment.
What is the performance impact?
.svg)
Best in class Performance: <0.2% CPU &<300MB RAM, when all modules are active. Raven is designed for high-throughput production environments. It analyzes execution at the library and function level using eBPF-based instrumentation, with negligible runtime overhead and no impact on application latency or stability.
What is the difference between ADR and WAF?
.svg)
A Web Application Firewall (WAF) filters and blocks malicious HTTP traffic at the network edge using predefined rules and signatures. Application Detection and Response (ADR), by contrast, operates inside the running application and analyzes real-time execution behavior, function calls, and application telemetry. While WAFs are effective at stopping known attack patterns, ADR provides deeper visibility into how attacks behave after reaching the application layer. This enables security teams to detect evasive threats, business logic abuse, and attacks that bypass perimeter defenses.
What is the difference between ADR and RASP?
.svg)
Runtime Application Self-Protection (RASP) focuses on automatically blocking or preventing malicious activity inside an application during execution. ADR complements this approach by prioritizing detection, investigation, and response through continuous runtime telemetry and behavioral analysis. Rather than simply stopping activity, ADR provides security teams with contextual insights into attack progression, affected functions, and attacker behavior. This broader visibility helps organizations investigate threats more effectively, reduce false positives, and identify sophisticated attacks that may not trigger prevention-based controls alone.
What is the difference between ADR and EDR?
.svg)
EDR wasn’t built for servers. ADR was.
EDR was born for workstations. But modern servers are different. They don’t just run operating systems; they run applications, APIs, frameworks, open-source libraries, and vulnerable functions. That is where today’s attacks happen. EDR can see that a process opened a shell, made a network connection, or behaved suspiciously. ADR goes deeper: it understands which application, library, function, and runtime path caused it - and can detect or prevent exploitation at the application layer.
EDR was born for workstations. But modern servers are different. They don’t just run operating systems; they run applications, APIs, frameworks, open-source libraries, and vulnerable functions. That is where today’s attacks happen. EDR can see that a process opened a shell, made a network connection, or behaved suspiciously. ADR goes deeper: it understands which application, library, function, and runtime path caused it - and can detect or prevent exploitation at the application layer.
Resources

Security
Not every CISO has the same security problem. Learn the key difference between infrastructure-first CISOs and software factory CISOs, and why code-aware runtime security matters for companies that build software.
Read more

Security
AI is turning exploit development into a repeatable assembly line. Learn how CVE-less attacks work and what security leaders must do differently at runtime.
Read more

Company News
Raven CEO Roi Abitboul explains why AI has broken traditional CVE-based security and why runtime visibility is the only defense model built for what comes next.
Read more

.svg)

